Digital security isn't improvised. It's built step by step.
Event overview
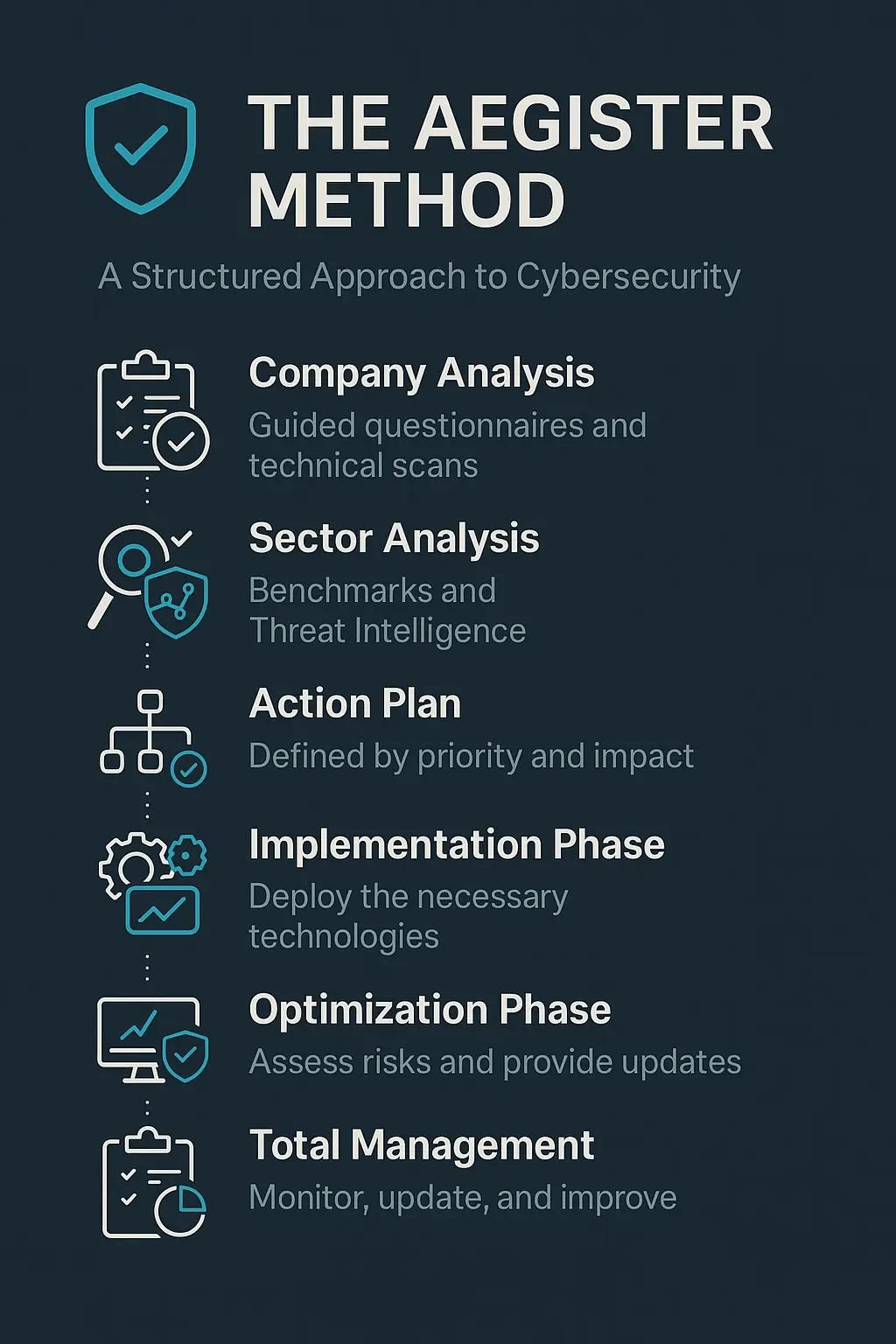
At Aegister, we follow a structured, personalized approach to cybersecurity. Every organization has unique characteristics, technologies, and risk levels. That's why applying a clear methodology makes the difference. With the NIS2 compliance deadline approaching, our method helps organizations meet regulatory requirements while maintaining robust security. Here's how we work:
What Aegister presented
With Aegister, cybersecurity is not just an option it's a strategic journey built on a proactive and protective foundation tailored to your operations.
Next steps
With Aegister, cybersecurity is not just an option it's a strategic journey built on a proactive and protective foundation tailored to your operations.
Key highlights
- The Aegister Method: A Structured Approach to Cybersecurity summarizes Aegister's event participation and key outcomes.
- The publication date for this update is 2025-04-29.
- The focus remains on international cybersecurity networking and service positioning.
Execution governance focus
For organizations applying this method, governance execution should be explicit: define control owners, escalation paths, evidence checkpoints, and review cadence before implementation starts. This keeps method adoption measurable and reduces drift between strategy and daily operations.
FAQ
What event is covered in this recap?
This article covers Aegister's participation in an international cybersecurity event highlighted in the post.
Where could visitors meet Aegister during the event?
Visitors could meet the team at stand SP64 during the event days.
How can organizations follow up after the event?
Organizations can continue the conversation through Aegister's official channels and published insights.
Official sources
Operational implications after the event
The Aegister Method: A Structured Approach to Cybersecurity should be used as an operational follow-up reference, not only as an event recap. Organizations evaluating similar initiatives should map discussed themes to internal priorities, decision owners, and next action windows so the event output becomes execution input.
- Extract practical control themes and assign review owners in GRC and security teams.
- Translate high-level takeaways into measurable implementation tasks and deadlines.
- Document stakeholder decisions and preserve evidence of why priorities were selected.
- Use recurring checkpoints to validate that post-event actions remain aligned with risk objectives.
Publication reference date: 2025-04-29. Keep timeline communication consistent with absolute calendar dates.